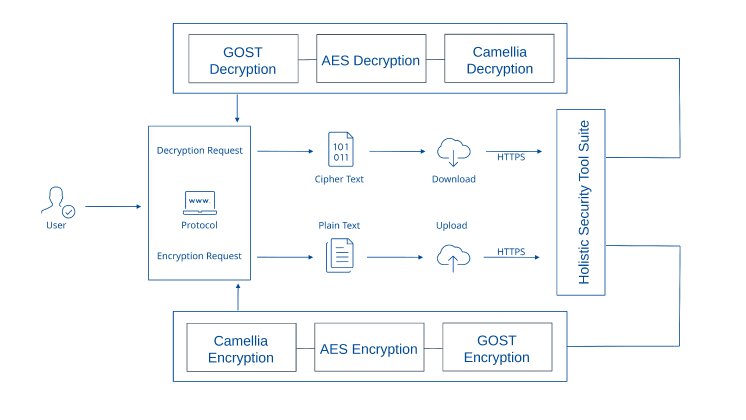
Standard encryption implementations rely on single algorithms, typically AES, which, while robust, create implicit dependencies on the cryptographic standards and certification authorities of specific nations. CypSec's approach transcends this limitation through deliberate algorithmic diversification. Every communication session initiates with HTTPS between user browser and CypSec's tool suite, then undergoes systematic chained cryptographic processing: Camellia (Japanese origin), AES (American origin), and GOST (Russian origin) operate in sequential layers, with each algorithm encrypting the output of its predecessor.
This architectural decision reflects strategic risk assessment rather than cryptographic novelty. Nation-state actors have demonstrated capability to influence standards bodies, certification processes, and potentially introduce weaknesses into nationally sponsored algorithms. By distributing trust across three distinct jurisdictional origins, CypSec ensures that compromise of any single national cryptographic ecosystem, through mathematical breakthrough, covert backdoor insertion, or standards manipulation, cannot alone breach CypSec's protective boundaries. An adversary capable of breaking AES would still face Camellia and GOST; capabilities against GOST would encounter AES and Camellia.
The technical implementation maintains operational efficiency despite cryptographic multiplicity. Hardware acceleration supports all three algorithms; modern processors execute the chained sequence with minimal latency overhead. Key management operates independently for each layer, with distinct key generation, distribution, and rotation procedures preventing common-mode failures. The architecture remains transparent to end users, HTTPS establishes the familiar browser security indicator, while internal chaining operates invisibly within CypSec's infrastructure boundaries.
The harmonization extends across CypSec's complete tool suite. Vulnerability management data, threat intelligence feeds, deception environment telemetry, active defense commands, and user authentication tokens all traverse the same multi-layered cryptographic substrate. This unified boundary eliminates the weak links that typically emerge at integration points between security tools, where data exits one encrypted domain and enters another, often in cleartext or with reduced protection.
For international customers, the standard delivers measurable strategic advantages. Cryptographic agility enables rapid response to emerging threats against specific algorithms: reconfiguration can prioritize or replace individual layers without architectural overhaul. Regulatory diversification satisfies compliance requirements across multiple jurisdictions simultaneously, from European data protection to Asian cryptographic regulations to national security frameworks. Most significantly, the architecture provides credible technical foundation for claims of vendor-independent security. Customers are not bound to the cryptographic fate of any single nation or standards body.
The implementation has undergone extensive validation through CypSec's research partnerships and red team exercises. Cryptographic analysis confirms that sequential application maintains security properties of the strongest individual algorithm while layering provides defense in depth. Performance testing demonstrates negligible impact on user experience or operational throughput. The chained standard now operates as default across all CypSec deployments, with customer visibility into cryptographic health and algorithm status through unified dashboard interfaces.